Simplifying Digital Operational Resilience for the EU Financial Sector.
Everyday activities of the financial sector are supported by complex Information and communication technology (ICT) systems supporting the introduction of many new digital services that enhance customer experience, increase the efficiencies of internal process, but at the same time introduce additional risks and vulnerabilities which may expose financial firms to cyber-attacks or other incidents that may disable important business services.
If these risks are not adequately managed, they may result in the suspension of financial services, which are frequently provided across national boundaries and have a significant impact on other businesses, industries, or even the EU economy. The possibility of such cross-border and cross-sectoral disruptions emphasizes the importance of the financial sector’s digital operational resilience.
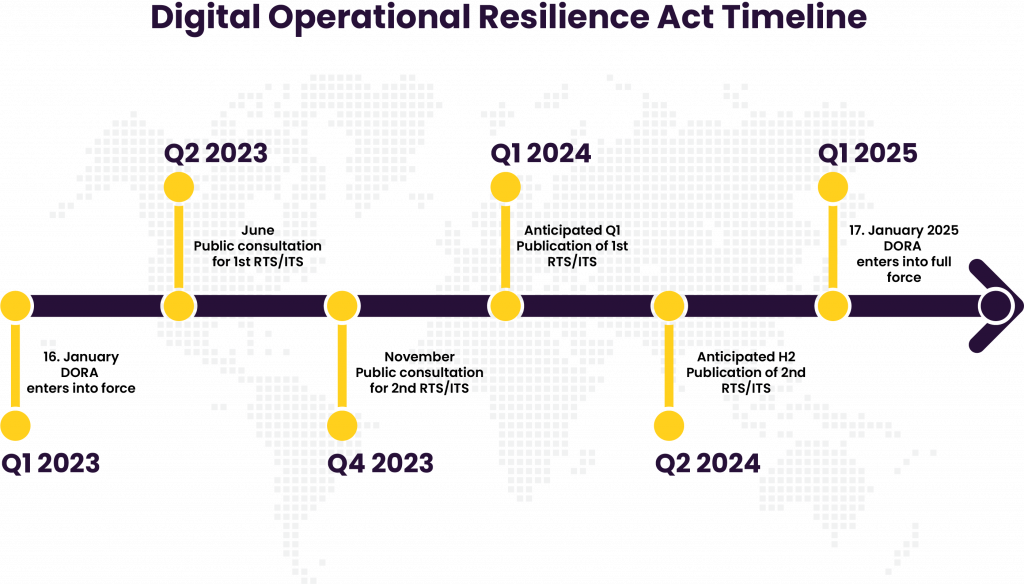
On 27 December 2022, the Digital Operational Resilience Act (DORA) was published in the Official Journal of the European Union as a measure to enhance the overall digital operational resilience of the EU financial sector and entered into force on 16 January 2023. DORA will come into full force from 17 January 2025.
If these risks are not adequately managed, they may result in the suspension of financial services, which are frequently provided across national boundaries and have a significant impact on other businesses, industries, or even the EU economy. The possibility of such cross-border and cross-sectoral disruptions emphasizes the importance of the financial sector’s digital operational resilience.
On 27 December 2022, the Digital Operational Resilience Act (DORA) was published in the Official Journal of the European Union as a measure to enhance the overall digital operational resilience of the EU financial sector and entered into force on 16 January 2023. DORA will come into full force from 17 January 2025.
Where does DORA fit in the context of existing EU Financial Directives?
DORA applies to upwards of 22,000 financial firms covering Banking & Payment Markets, Asset Management, Investment Services, Insurance, and forms part of a wider EU Digital Finance package as well as linking with European measures on cyber security and the European strategy for data. Of course, regulation in the financial sector is not new and the Digital Operational Resilience Act DIRECTIVE sits at a higher level in the context of the DORA with the legal objective of strengthening digital operational resilience through the amendment of certain EU Financial Sector Directives, such as, CRD IV and PSD2 (Banking & Payment Markets), Solvency II (Insurance), UCITS IV and AIFMD (Asset Management) and MiFID II (Investment Services).
How will DORA compliance work in practice?
The Digital Operational Resilience Act REGULATION defines a detailed and complete framework of rules for the identification and management of ICT and Cyber risk, establishing obligations regarding periodic testing of infrastructures and the use of strategies, policies, processes, tools and reporting to address all facets of digital operational resilience. Within the regulations there are two types of standards: the regulatory technical standards (RTS), which are adopted by the Commission by means of a delegated act and the implementing technical standards (ITS), which are adopted by means of an implementing act. The ITS aim to set in place uniform reporting requirements to ensure fair conditions of competition between comparable groups of financial firms.
Digital Operational Resilience Testing
Although the level of testing needed may vary depending on the kind, size, and complexity of the financial firm under consideration, independent testing and self-assessment will always be essential to evaluate readiness for addressing ICT-related catastrophes and to spot flaws, shortcomings, and gaps in digital operational resilience. Certain financial companies will also be required to do more advanced testing at least every three years in addition to the yearly testing.
How can Cristie Data help your Digital Operational Resilience strategy?
Cristie Data bring decades of Data Management and Data Security experience into play and work with leading technology partners in areas including Zero Trust Data Protection, Managed Security Operations, large scale System Recovery and Simulated Recovery Testing. Our financial sector team can advise on appropriate technologies and processes that can simplify operational resilience testing, self-assessment regulatory reporting, and the orchestration of ICT system recovery at scale. Contact us to discuss your current challenges and milestones required in meeting the 17 January 2025 deadline.