We added SPFS file system as an option to Cristie backup solution. In IBM’s enterprise backup solution Spectrum Protect, we can do even more workloads – e.g. B. in MySQL, PostgreSQL and Casandra – protect. But what is the difference between Spectrum Scale and SPFS? Can SPFS be used instead of Spectrum Scale? Or should you have both? To understand the differences, we explain the basics of Spectrum Scale and SPFS in this article.
What is spectrum scale?
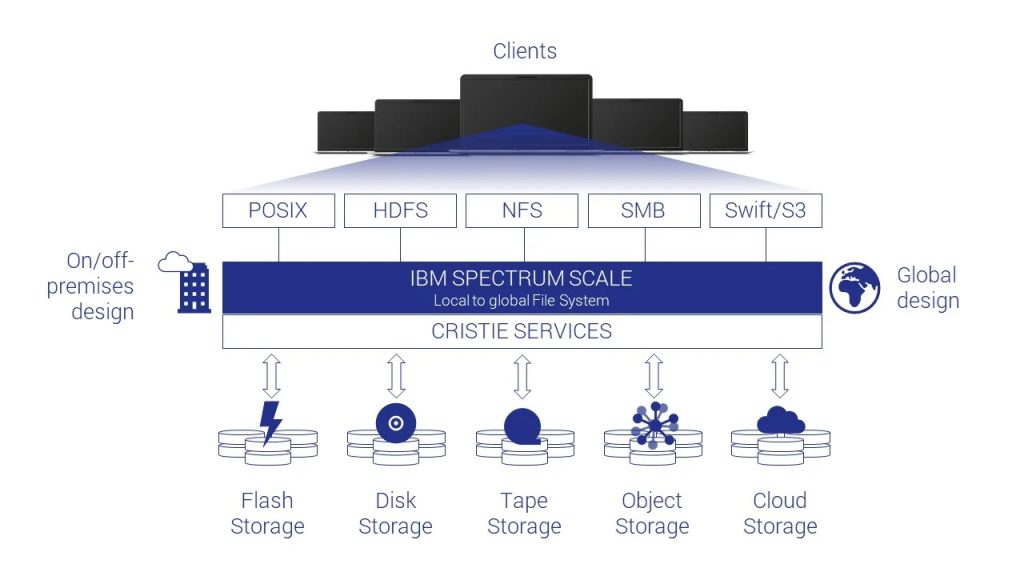
IBM Spectrum Scale is a global file system with a single namespace. This allows files to be shared between different servers, clients and applications. So everyone can read and edit the same file at the same time at any time without interfering with each other.
Spectrum Scale is one of the cluster file systems that can be distributed across multiple nodes. This makes the file system large enough for most of us, even if the data volume is a yottabyte – which is really an incredible amount of data. At Cristie, we don’t currently know of any company that manages a septillion bytes. Even the analysts at IDC are forecasting ‘only’ a total volume of 163 zettabytes worldwide by 2025.
A major advantage of cluster file systems is the ability to share them with different clients. This means that an application or a single user has unlimited storage space available. The data to be backed up can be written to the Spectrum Scale file system via a local mount point, via shares (NFS / CIFS) or as an object (S3).
Data is managed using policies. This also allows data to be automatically moved to different storage levels. This so-called auto tiering ensures optimal use of the available media. Hot data – data that needs to be accessed quickly and often – ends up on SSDs and cold data on cheaper but slower HDDs or tapes. Data can also be backed up or outsourced in the cloud via the S3 interface. Spectrum Scale supports both private and public cloud computing platforms. One of the tiers of storage can also be IBM Spectrum Protect.
Spectrum Scale is one of the cluster file systems that can be distributed across multiple nodes. This makes the file system large enough for most of us, even if the data volume is a yottabyte – which is really an incredible amount of data. At Cristie, we don’t currently know of any company that manages a septillion bytes. Even the analysts at IDC are forecasting ‘only’ a total volume of 163 zettabytes worldwide by 2025.
A major advantage of cluster file systems is the ability to share them with different clients. This means that an application or a single user has unlimited storage space available. The data to be backed up can be written to the Spectrum Scale file system via a local mount point, via shares (NFS / CIFS) or as an object (S3).
Data is managed using policies. This also allows data to be automatically moved to different storage levels. This so-called auto tiering ensures optimal use of the available media. Hot data – data that needs to be accessed quickly and often – ends up on SSDs and cold data on cheaper but slower HDDs or tapes. Data can also be backed up or outsourced in the cloud via the S3 interface. Spectrum Scale supports both private and public cloud computing platforms. One of the tiers of storage can also be IBM Spectrum Protect.
Spectrum Scale is scale-out file system.
What is SPFS?
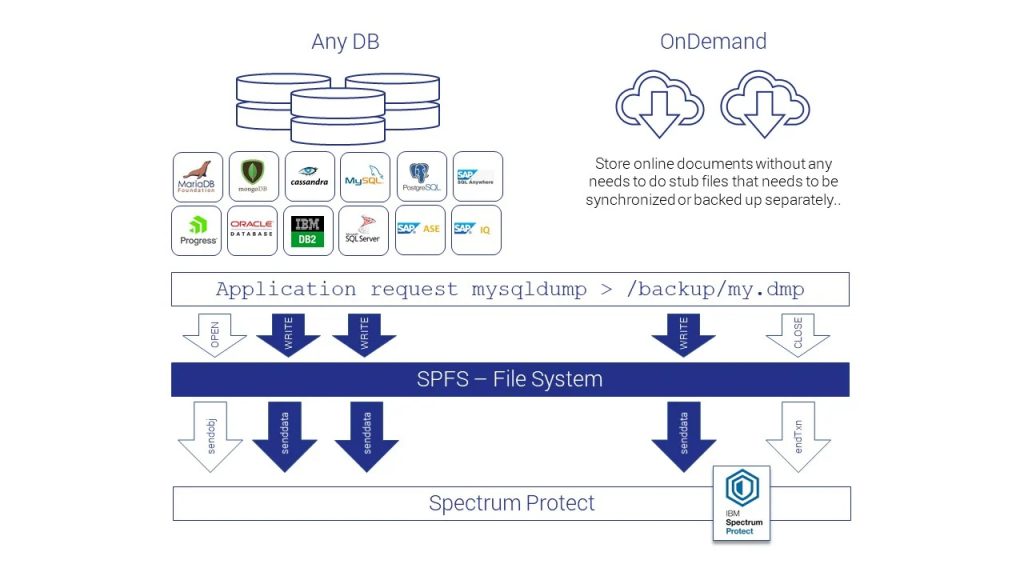
Our SPFS stands for Spectrum Protect Filesystem and has nothing to do with the Russian SWIFT clone. SPFS is a virtual file system that, as a backup and archive file system, provides useful features such as WORM (Write Once Read Many), versioning, encryption, data redundancy, data reduction techniques, and data filtering. In fact, SPFS is just a small binary that translates file system operations into API calls for Spectrum Protect. SPFS does not require any local storage, even temporary. All I/O operations are sent directly to the Spectrum Protect server. In this way, the backup and recovery tools currently used in the company can be used as usual. That saves time and money.
SPFS is very easy to use and behaves like a normal Linux file system. Backups can be viewed using the “ls” commands or can be viewed using small scripts such as; pg_dump> /backup/pg.dmp, automate. All other commands such as “cp”, “rm”, “mkdir”, “rmdir” etc. also work as usual. That just makes it easy to integrate SPFS into any application. In addition, SPFS caches metadata and has read-ahead technology. This saves valuable time when querying or restoring.
Data is transferred, deduplicated and compressed asynchronously. The file system can be provided as a backup or archive. No special agents need to be used to protect databases. Versioning provides additional security: If a file is overwritten, SPFS automatically renames the old file in Spectrum Protect.
SPFS is very easy to use and behaves like a normal Linux file system. Backups can be viewed using the “ls” commands or can be viewed using small scripts such as; pg_dump> /backup/pg.dmp, automate. All other commands such as “cp”, “rm”, “mkdir”, “rmdir” etc. also work as usual. That just makes it easy to integrate SPFS into any application. In addition, SPFS caches metadata and has read-ahead technology. This saves valuable time when querying or restoring.
Data is transferred, deduplicated and compressed asynchronously. The file system can be provided as a backup or archive. No special agents need to be used to protect databases. Versioning provides additional security: If a file is overwritten, SPFS automatically renames the old file in Spectrum Protect.
And now what is the difference between SPFS and Spectrum Scale?
SPFS uses the Spectrum Protect Backup Archive Client API to log in. The little helper can read and write to a Spectrum Protect Node file area. However, this only works 1:1. Each SPFS installation requires its own node in Spectrum Protect – unlike Spectrum Scale which is shared between multiple hosts.
Each SPFS installation requires its own node in Spectrum Protect.
#atyourservice
#atyourservice

